How to Fix 'an error is expected but got nil'
In the intricate world of software development, few messages can induce as much immediate frustration and bewilderment as "an error is expected but got nil." This seemingly innocuous phrase, often encountered in various programming environments, particularly those with strong type systems or explicit error handling conventions, signals a fundamental mismatch between what the code anticipates and what it actually receives. It's a stark reminder that even the most meticulously crafted systems can stumble when a crucial piece of information – an error object – simply vanishes into the ether, replaced by an empty void. This isn't merely a minor bug; it often points to deeper architectural assumptions, faulty external integrations, or lapses in defensive programming that can lead to unpredictable system behavior, data corruption, or even complete service outages.
The journey to understanding and ultimately resolving "an error is expected but got nil" is an essential rite of passage for any developer striving to build robust and resilient applications. It demands a meticulous blend of diagnostic prowess, a deep understanding of language semantics, and a commitment to best practices in error handling and system design. This comprehensive guide will dissect the multifaceted nature of this error, exploring its origins across various programming paradigms, identifying common scenarios where it manifests, and outlining a systematic approach to diagnosis, debugging, and ultimately, prevention. We will delve into how critical components like an api gateway, an llm gateway, and principles within a mcp (Multi-Cloud Platform) architecture play crucial roles both in causing and mitigating such issues. By the end, you will be equipped with the knowledge and strategies to not only fix this specific error but to cultivate a mindset that anticipates and gracefully handles the inevitable imperfections of distributed systems.
Understanding the Void: What 'nil' Truly Signifies in Error Handling
To effectively combat "an error is expected but got nil," we must first deeply understand the concept of nil itself and its profound implications within the context of error management. In many programming languages, nil (or null, None, etc.) represents the absence of a value. It's a placeholder for "nothing," indicating that a variable or pointer does not refer to any object or memory location. While this concept is fundamental, its interaction with error handling mechanisms is where the specific problem statement arises.
Consider languages like Go, where functions often return two values: a result and an error (e.g., (result, error)). The convention dictates that if an operation succeeds, the result will contain a valid value, and error will be nil. Conversely, if an operation fails, result might be a zero-value or nil, and error will contain a non-nil error object detailing what went wrong. The error message "an error is expected but got nil" explicitly tells us that the code expected a non-nil error object in the error return position, but instead received nil. This suggests that the function or operation logically failed or entered a state where an error should have been generated, but for some reason, the mechanism responsible for creating and returning that error object either failed to execute, was bypassed, or returned an unexpected nil.
This scenario is particularly insidious because it represents a silent failure or an incomplete error reporting mechanism. Instead of crashing immediately with a clear stack trace pointing to the origin of an unhandled exception, the system continues, believing no error occurred, only for a subsequent part of the code—the part expecting an error—to detect this anomaly. This delay in detection can obscure the true root cause, making debugging a significantly more arduous task. The nil in the error position effectively acts as a ghost, an invisible omission that corrupts the expected flow of error propagation, leaving dependent components in a state of confusion and potential instability. It’s a violation of the contract between the caller and the callee, where the callee promises an error object on failure but delivers emptiness.
The implications of such a nil error are far-reaching. In a best-case scenario, it might lead to a controlled fallback mechanism. In a worst-case scenario, it could cause critical business logic to operate on incomplete or invalid data, trigger cascading failures across microservices, or expose security vulnerabilities. For instance, if a database query fails to find a user but returns nil instead of an error object (and the nil is interpreted as "user not found" when it should be "database connection failed"), subsequent logic might mistakenly create a new user or grant unauthorized access. This is why a deep dive into the nuances of nil and its interaction with error interfaces is paramount for any developer aiming to build resilient systems.
Common Scenarios Leading to 'an error is expected but got nil'
The error "an error is expected but got nil" rarely appears in isolation; it is usually a symptom of a deeper issue within the application's logic, its interaction with external systems, or its underlying infrastructure. Understanding the common scenarios where this error typically arises is the first step toward effective diagnosis and resolution. Each scenario often reflects a specific type of breakdown in communication or expectation within a software system.
1. Misconfigured or Failing API Interactions
One of the most frequent culprits behind this error lies in the realm of API interactions, especially in distributed systems. When your application communicates with external services, microservices, or even internal APIs, it relies on specific contracts for requests and responses, including how errors are reported.
- External Service Failures: An external API might encounter an internal server error (e.g., HTTP 500) but, due to poor implementation, return an empty response body or an unexpected structure instead of a standardized error object. Your client code, expecting a JSON error payload on a non-2xx status, might parse the empty body as
niland then fail when trying to extract an error message from it, effectively leading toan error is expected but got nilin the error handling path. - Incorrect Request/Response Handling: The client-side code might be incorrectly configured to handle certain HTTP status codes. For example, if a 404 (Not Found) or 401 (Unauthorized) status is received, the client library might correctly identify it as an error but fail to map it to a concrete error object, leaving the error variable
nil. This is particularly common when developers override default error deserialization logic without fully accounting for all possible non-success responses. - Timeouts and Network Issues: During network disruptions or service timeouts, an HTTP client library might fail to receive any response. While some libraries are designed to return a specific timeout error, others might return
nilor an unhandled exception, leading tonilin the error handling path if not caught and transformed appropriately. The underlying connection might simply drop, leaving the calling code with an unfulfilled expectation of some kind of error object. - Mismatched API Versions or Contracts: If the client is calling an older or newer version of an API than it expects, the server might return an unfamiliar response format for errors. The client's deserialization logic, unable to parse this new format into its expected error object, might default to
nilfor the error part, signaling that "no recognizable error object was found."
A robust api gateway can significantly mitigate these issues. By standardizing error formats, enforcing schemas, and providing circuit-breaking capabilities, an api gateway ensures that even if a backend service fails unpredictably, the consuming application receives a consistent, well-formed error message rather than a nil or an ambiguous response. This acts as a crucial layer of abstraction, transforming potentially chaotic backend errors into predictable, consumable error objects for the frontend.
2. Database Operations Going Awry
Interactions with databases are another fertile ground for "an error is expected but got nil." Database operations are inherently prone to various failure modes, and how these failures are communicated back to the application layer is critical.
- Connection Failures: If the application loses its connection to the database, or fails to establish one initially, the database driver or ORM (Object-Relational Mapper) is expected to return a connection error. However, in some edge cases or specific library implementations, a lost connection might result in an operation appearing to complete without an explicit error object being returned, leading to a
nilerror. - Query Execution Errors: SQL syntax errors, invalid table/column names, or constraint violations (e.g., trying to insert a duplicate primary key) should all result in specific database errors. If the ORM or raw driver doesn't correctly capture and wrap these underlying errors, or if there's a bug in the error-mapping layer, the application might receive
nilinstead of a detailed error object. - Record Not Found vs. Query Error: Sometimes, a query that returns no rows (e.g.,
SELECT * FROM users WHERE id = 123and user 123 doesn't exist) is distinct from a query that fails (e.g.,SELECT * FROM non_existent_table). An ORM might returnnilfor the object when a record isn't found, which is correct behavior. However, if the calling code expects an error object specifically to distinguish between "not found" and "query failed," and the ORM only providesnilfor both success-no-rows and actual failure, it can lead to confusion and the perception of an "expected error but got nil" situation. The developer might be looking for a specificErrNotFounderror, but instead seesnil, even though a logical "not found" scenario occurred.
3. File System and I/O Operations
Working with the file system also presents opportunities for this error, particularly when dealing with permissions, existence, or corruption.
- File Not Found: While standard file I/O libraries generally return a clear "file not found" error, some custom wrappers or higher-level abstractions might misinterpret this as a non-error condition or fail to propagate the underlying system error correctly. The function might return an empty file handle or an object representing "nothing" (
nil), when the caller expected anos.ErrNotExisttype of error. - Permission Issues: Lack of read/write permissions for a file or directory should result in a permission denied error. If the I/O operation silently fails or returns
nilin its error slot due to an incomplete error handling path within a library, it can create a similar problem. - Corrupted Files or Devices: Reading from a corrupted file or an unmounted device can sometimes lead to unexpected behavior in I/O operations. The system might not immediately generate a clear error but instead return an incomplete read or a
nilbyte slice, leading tonilin the error return if the underlying I/O abstraction isn't robust.
4. Concurrency and Goroutines (Specific to Go-like Contexts)
In concurrent programming environments, especially those like Go with goroutines and channels, error propagation is a critical concern that can lead to nil errors if not handled carefully.
- Uncaptured Goroutine Errors: If a goroutine starts a long-running operation that eventually fails, but its error return is not correctly channeled back to the main thread or an error aggregation mechanism, the main thread might conclude that the operation completed without error (receiving
nilwhere an error should have been) or simply never receive an error at all. This often happens when errors are logged internally by the goroutine but not propagated outwards. - Channel Misuse: Closing a channel prematurely or attempting to read from a closed channel without proper checks can lead to unexpected zero values or
nils, particularly if the values being sent through the channel are errors themselves. If a channel intended for error propagation closes before an error is sent, the receiver might getnilinstead of the expected error. - Race Conditions in Error Reporting: In complex concurrent systems, race conditions can occur where one part of the system tries to report an error while another part concurrently tries to signal success or simply closes the error reporting channel. This can result in the error being lost or overwritten, leaving a
nilin its place.
5. Third-Party Libraries and SDKs
The integration of external libraries and Software Development Kits (SDKs) introduces a layer of dependency that can be a source of nil errors.
- Improper Initialization: Many libraries require specific initialization steps. If a library is not initialized correctly, subsequent calls to its functions might return
nilinstead of a clear "not initialized" error. This is because the internal state necessary to generate a proper error object might not even be set up. - Version Mismatches or Bugs: A bug in a third-party library, especially in how it handles internal failures, can lead to it returning
nilwhere an error object is expected. This could be due to an oversight by the library developer or an unexpected interaction with your specific runtime environment. - Poorly Documented Behavior: Some SDKs might have undocumented behaviors where certain functions return
nilfor specific failure conditions rather than a well-defined error, forcing developers to infer behavior or delve into the SDK's source code.
6. Configuration Management Challenges
Configuration is the backbone of any application, and its mismanagement can easily lead to nil errors.
- Missing or Malformed Configurations: If the application expects a specific configuration value (e.g., a database connection string, an API key) but it's missing or incorrectly formatted, the parsing logic might fail to produce an error object. Instead, it might return a
nilconfiguration struct or anilvalue for the missing field. Subsequent code trying to use thisnilvalue will then fail, potentially leading to the "expected error but got nil" if the initial configuration loading process didn't properly surface the error. - Environment Variable Issues: Applications heavily rely on environment variables in containerized or cloud-native deployments. If a critical environment variable is unset, a function attempting to retrieve it might return an empty string or
nilinstead of a clear error, especially if the getter function is poorly implemented. - Multi-Cloud Platform (MCP) Complexity: In a mcp environment, managing configurations across different cloud providers (AWS, Azure, GCP, etc.) introduces significant complexity. Each cloud might have its own secret management, key-value stores, or configuration services. Inconsistent configuration patterns or subtle differences in how secrets are retrieved could lead to
nilvalues being passed to services expecting valid configurations, eventually manifesting asan error is expected but got nilwhen a component tries to initialize itself with these empty values. A unified configuration management strategy within an mcp is critical to avoid these discrepancies.
7. Large Language Model (LLM) Interactions
With the rise of AI-powered applications, interactions with Large Language Models introduce a new set of challenges, particularly when integrating them via an llm gateway.
- API Rate Limits and Quotas: LLM providers often impose strict rate limits and usage quotas. If an application exceeds these, the LLM API might return an error. However, a client library or an llm gateway that isn't specifically designed to handle these errors might misinterpret the response or fail to map it to a proper error object, resulting in a
nilerror in the application. - Invalid Prompts or Model Inputs: Sending an malformed or excessively long prompt, or providing input that violates the model's constraints, should trigger an error from the LLM. If the llm gateway or the direct API client doesn't properly parse these provider-specific errors into a unified error format, the application might receive
nilwhere a clear "invalid input" error is expected. - Model Availability and Health: LLMs, especially those hosted by third parties, can experience downtime or performance degradation. An llm gateway might retry requests or implement fallbacks. However, if these mechanisms fail, and the underlying LLM API returns an ambiguous
nilor an unparseable response during a critical failure, the application will struggle to interpret the true nature of the problem. A robust llm gateway should standardize these underlying failures into a consistent error structure.
By recognizing these common scenarios, developers can better target their diagnostic efforts, systematically tracing the flow of data and error objects through their applications and across system boundaries. The consistent theme is a breakdown in the expected contract of error reporting, where an empty value (nil) replaces a meaningful error object, creating a silent failure that can be deceptively hard to pinpoint.
Diagnostic Strategies and Tools: Unraveling the Mystery
When confronted with "an error is expected but got nil," the initial feeling can be overwhelming, akin to searching for a needle in a haystack where the needle is invisible. However, a structured diagnostic approach, combined with the right tools, can systematically peel back the layers of complexity and reveal the root cause. This section outlines a comprehensive set of strategies, moving from high-level code analysis to deep-dive runtime inspection.
1. Meticulous Code Review and Static Analysis
Before even running the code, a thorough manual and automated code review can illuminate potential culprits. This is often the most cost-effective diagnostic step.
- Tracing Execution Paths: Start by identifying the exact line of code where the error message
an error is expected but got niloriginates. Then, meticulously trace back the execution path to understand hownilmight have arrived in the error variable. Look for function calls whose return types include an error, and investigate where those errors are assigned or ignored.- Specifically, look for: Functions that should return an error but might have a conditional path where they return
nilprematurely or unintentionally. Also, look for places where an error from a nested call is passed upwards, but perhaps only conditionally, leaving anilin other branches.
- Specifically, look for: Functions that should return an error but might have a conditional path where they return
- Identifying
nilAssignments: Search for all instances where the variable that eventually becomesnil(and is expected to be an error) is explicitly assignednil. This can happen if a fallback mechanism mistakenly returnsnilon failure, or if an error variable is reset. - Function Signature Compliance: Verify that all functions returning an error actually return a concrete error object on failure. In many languages, returning
nildirectly as an error is acceptable for "no error," but if a failure did occur, it must be a non-nilerror type. Check for interfaces or abstract error types where the concrete implementation might default tonilin an unexpected scenario. - Static Analysis Tools: Leverage linters and static analysis tools specific to your language (e.g.,
golangci-lintfor Go, RuboCop for Ruby, ESLint for JavaScript). Many of these tools have rules designed to catch common error-handling mistakes, such as ignored errors or assignments that could lead tonilin unexpected places. They can flag suspiciousif err != nilblocks that might be missing necessaryreturn errstatements.
2. Comprehensive Logging and Observability
Good logging practices are the bedrock of effective debugging in distributed systems. When an error like this occurs, well-placed logs can pinpoint the exact moment and context of the nil anomaly.
- Structured Logging: Implement structured logging (e.g., JSON logs) throughout your application. This allows for easy parsing and querying of logs, especially when using log management platforms. Key pieces of information to log include:
- Function entry and exit points.
- Values of critical variables, especially error objects and their types.
- Results of external API calls, including HTTP status codes and partial response bodies.
- Database query results and any errors returned by the driver/ORM.
- Contextual Logging: Always enrich your log messages with contextual information: request IDs, user IDs, transaction IDs, service names, and hostnames. This is invaluable for tracing an event through a complex microservices architecture.
- Tracepoints Around Suspect Calls: Temporarily add detailed log statements immediately before and after any function call that you suspect might be returning
nilinstead of an error. Log the exact values returned, including the error variable. This can quickly narrow down the problematic function. - Distributed Tracing: For microservices architectures, distributed tracing tools (like Jaeger, OpenTelemetry, Zipkin) are indispensable. They allow you to visualize the entire request flow across multiple services, highlighting where failures or unexpected
nilvalues might be introduced. You can see which service call returned an unexpectedniland trace it back to its origin. - Metrics and Alerts: While not directly for debugging
nilerrors, anomalous metrics (e.g., sudden drop in successful API calls, increase in HTTP 500s from an internal service) can alert you to a problem that might be manifesting asan error is expected but got nildownstream. Setting up alerts for specific error patterns in logs is also crucial.
3. Debugging Tools and Interactive Inspection
When logs aren't enough, interactive debugging allows you to step through the code execution and inspect variable states in real-time.
- IDE Debuggers: Modern Integrated Development Environments (IDEs) offer powerful debugging capabilities. Set breakpoints at the line where the error occurs and then step backward through the call stack. Inspect the value of the error variable at each step to see precisely where it transitions from a concrete error to
nil.- Tip: Pay close attention to conditional branches. The error might be correctly set in one branch but explicitly or implicitly cleared to
nilin another.
- Tip: Pay close attention to conditional branches. The error might be correctly set in one branch but explicitly or implicitly cleared to
- Remote Debugging: For applications running in containerized environments (Docker, Kubernetes) or on remote servers, configure remote debugging. This allows you to attach your IDE debugger to a running process, providing the same level of inspection as local debugging without needing to reproduce the issue locally.
- Print Debugging (Cautiously): As a last resort, or for quick checks in simple scenarios, strategic
printorlogstatements can be used. However, this should be temporary and removed after debugging, as excessive print statements can clutter logs and affect performance.
4. Robust Unit and Integration Testing
A well-designed test suite can prevent nil errors from reaching production and help pinpoint them quickly during development.
- Error Condition Testing: Write unit tests that specifically target error conditions. For any function that returns an error, write tests that:
- Verify it returns a non-
nilerror when an expected failure condition occurs (e.g., invalid input, external service error). - Verify the type of the error (e.g.,
os.IsNotExist(err)) is correct. - Use mock objects or dependency injection to simulate scenarios where dependencies might return
nilin their error slot.
- Verify it returns a non-
- Integration Tests: Create integration tests that exercise the interactions between your services and external dependencies (databases, APIs). These tests can expose
nilerrors that arise from the complex interplay of components, such as when an api gateway transforms an error unexpectedly, or an llm gateway misinterprets a model's failure response. - Fuzz Testing (Advanced): For critical components, fuzz testing can randomly generate inputs to uncover unexpected code paths that might lead to
nilerrors under unusual conditions.
5. Network Monitoring and API Inspection Tools
When the error originates from interactions with external services, network tools are invaluable.
- HTTP Client Interceptors/Middlewares: Implement custom interceptors or middlewares in your HTTP client (e.g.,
http.Clientin Go, Axios interceptors in Node.js) to log or inspect every request and response. This allows you to see the raw HTTP status code, headers, and body received from the external service before your application's error handling logic processes it. - Proxy Tools (e.g., Fiddler, Charles, mitmproxy): Use HTTP proxy tools to intercept and inspect network traffic between your application and external APIs. This provides an independent view of the exact responses received, helping to determine if the external service is truly returning
nilor an unexpected format, or if the issue lies within your client-side parsing. curland Postman/Insomnia: Manually replicate the API call usingcurlor a tool like Postman. This helps isolate whether the issue is with your application's client implementation or the external API's behavior. Ifcurlshows a valid error response, the problem is likely in your application's processing.
By systematically applying these diagnostic strategies, developers can transform the daunting task of fixing "an error is expected but got nil" into a manageable, logical problem-solving exercise. The key is to gather as much context as possible, starting broad and then narrowing down to the exact point of failure.
| Diagnostic Strategy | Key Activities | Expected Output / Benefit | Common Tools / Techniques |
|---|---|---|---|
| Code Review | Trace execution paths, identify nil assignments, check function contracts. |
Pinpoint logical flaws, potential nil injection points. |
Manual inspection, Peer review, Static analysis tools (linters) |
| Logging/Observability | Implement structured logs, add contextual info, use distributed tracing. | Real-time insights into system flow, error propagation across services. | ELK Stack, Grafana, Jaeger, OpenTelemetry, Sentry, Prometheus |
| Interactive Debugging | Set breakpoints, step through code, inspect variable states. | Precise state inspection at exact moments of execution. | IDE debuggers (VS Code, IntelliJ), GDB, Delve (Go) |
| Testing | Write unit/integration tests for error paths, use mocks. | Proactive error detection, regression prevention, isolated failure reproduction. | Jest, Go's testing, NUnit, JUnit |
| Network Monitoring | Intercept HTTP requests/responses, analyze traffic. | Verify external API responses, identify network-level issues. | curl, Postman, Fiddler, Charles Proxy, mitmproxy |
APIPark is a high-performance AI gateway that allows you to securely access the most comprehensive LLM APIs globally on the APIPark platform, including OpenAI, Anthropic, Mistral, Llama2, Google Gemini, and more.Try APIPark now! 👇👇👇
Resolution Techniques and Best Practices: Building Resilience
Once the root cause of "an error is expected but got nil" has been identified, the next critical step is to implement robust resolution techniques and adopt best practices that prevent its recurrence. This involves a multi-faceted approach, encompassing changes in coding style, architectural considerations, and leveraging specialized tools like an api gateway and an llm gateway.
1. Defensive Programming: Always Expect the Unexpected nil
The most fundamental principle to combat nil errors is defensive programming. Assume that any function or operation might return nil unexpectedly, even if it "shouldn't."
- Explicit
nilChecks: For every function call that returns a value and an error, always check both. If the error is non-nil, handle it immediately and return it or propagate it. If the value might benileven when the error isnil(e.g.,(user, nil)where user isnilbecause no user was found), explicitly check fornilon the value before attempting to dereference it.go // Example in Go-like pseudocode user, err := getUserByID(userID) if err != nil { // Handle actual error, e.g., database connection issue log.Errorf("Failed to retrieve user: %v", err) return nil, err } if user == nil { // Handle "user not found" as a distinct logical outcome return nil, ErrUserNotFound // Define a specific error for this case } // Proceed with valid user object - "Null Object" Pattern: Instead of returning
nilfor an object that wasn't found, consider returning a "null object" that implements the same interface but performs no-op operations or returns default values. This can simplify client code by avoiding numerousnilchecks, especially in display or aggregation logic. However, this pattern is less suitable for error reporting itself. - Optionals/Maybes: In languages that support them (e.g., Swift's Optionals, Rust's Option and Result enums, Java's Optional), use these constructs explicitly to represent the potential absence of a value or the possibility of failure. This forces developers to handle both
Some(value)andNone(orOk(value)andErr(error)) explicitly, eliminating accidentalnildereferences. - Early Exits/Returns: When an error condition or a
nilvalue is detected, perform an early exit from the function or method. This prevents subsequent logic from executing with invalid data and simplifies the control flow.
2. Robust Error Handling and Propagation
A sophisticated error handling strategy is paramount to ensure that meaningful error information is always propagated, rather than being swallowed or replaced by nil.
- Error Wrapping and Context: When an error is received from a downstream function or external service, wrap it with additional context before propagating it upwards. This provides a rich trail of information for debugging.
go // Example in Go-like pseudocode _, err := externalAPICall() if err != nil { // Wrap the error with specific context about this call return fmt.Errorf("failed to call external API: %w", err) } - Custom Error Types: Define specific custom error types (or error constants) for distinct failure conditions within your application. This allows upstream callers to precisely identify and handle different types of errors (e.g.,
ErrUserNotFound,ErrInvalidInput,ErrServiceUnavailable). This avoids the ambiguity of a genericniland allows for more nuanced error recovery. - Centralized Error Handling: Implement a centralized mechanism for handling and logging errors, especially in web applications or microservices. This ensures consistency in error responses (e.g., always returning a standardized JSON error payload for API clients) and prevents individual endpoints from returning malformed or
nil-like errors. - Idempotent Operations and Retries: For transient errors (like network glitches that might cause an external API to return
niltemporarily), implement idempotent operations and strategic retry mechanisms with exponential backoff. However, be careful to differentiate between transient errors and permanent failures to avoid infinite retries.
3. Input Validation at All Boundaries
Many nil errors originate from unexpected or invalid input that causes downstream functions to fail in ways they weren't designed to handle.
- Strict Input Validation: Validate all incoming data at the earliest possible point: API request bodies, query parameters, function arguments, configuration values. Reject invalid input with clear, descriptive error messages. This prevents
nilor malformed values from propagating deep into the system. - Schema Enforcement: Use schema validation (e.g., OpenAPI/Swagger for REST APIs, Protobuf for gRPC, JSON Schema) to enforce data contracts. This ensures that incoming data conforms to expected structures and types, reducing the likelihood of
nilvalues appearing where concrete data is expected.
4. Dependency Management and Testing
Maintain a healthy dependency ecosystem and integrate rigorous testing to catch nil errors early.
- Keep Dependencies Updated: Regularly update third-party libraries and SDKs to benefit from bug fixes and improved error handling. Be cautious, however, and review changelogs for breaking changes.
- Vendor Dependencies: If using Go or similar languages, vendor your dependencies to ensure reproducible builds and prevent unexpected changes in behavior from external libraries.
- Continuous Integration/Continuous Deployment (CI/CD): Integrate robust unit, integration, and end-to-end tests into your CI/CD pipeline. This ensures that any change that introduces a
nilerror is caught before it reaches production. Automate these checks aggressively.
5. Leveraging API Management Platforms (APIPark)
For distributed systems, especially those interacting with numerous services and AI models, an advanced api gateway and management platform is invaluable in preventing and managing nil errors.
This is where a solution like APIPark truly shines. APIPark, an open-source AI gateway and API management platform, provides a critical layer of abstraction and control that can significantly reduce the occurrence and impact of "an error is expected but got nil" errors, particularly in complex, modern application architectures.
- Unified API Format for AI Invocation: One of APIPark's key features is its ability to standardize the request data format across all AI models. This directly addresses the problem of
nilerrors arising from inconsistent or unexpected responses from various LLM providers. If an underlying AI model returns an ambiguousnilor an unparseable error, APIPark can intercept, transform, and normalize that into a consistent, well-defined error object that your application expects. This ensures that your application always receives a predictable error structure, preventing the "expected error but got nil" scenario that can occur when dealing with diverse AI service APIs. By abstracting away the nuances of different LLM providers, APIPark ensures that even if a specific LLM returns an unexpectednilas part of its internal failure, your application gets a proper error. - End-to-End API Lifecycle Management: APIPark assists with managing the entire lifecycle of APIs, including design, publication, invocation, and decommission. This comprehensive management allows for the enforcement of strict API contracts and error response schemas at the api gateway level. By regulating API management processes, APIPark helps ensure that all APIs, both internal and external, adhere to a defined error handling standard. This means if a backend service (even one that's poorly implemented) tries to return
nilwhere an error object is expected, the api gateway can catch this, log it, and return a standardized error to the client, preventing the downstream application from receiving the ambiguousnil. - Detailed API Call Logging: APIPark provides comprehensive logging capabilities, recording every detail of each API call. This is an absolute game-changer for diagnosing
nilerrors. Ifan error is expected but got niloccurs, you can leverage APIPark's detailed logs to trace the exact request and response that led to the issue. You can see precisely what the backend service returned before your application processed it, helping to identify whether theniloriginated from the backend or from your client-side parsing logic. This granular visibility significantly reduces debugging time. - Prompt Encapsulation into REST API: By encapsulating prompts into REST APIs, APIPark provides a consistent interface to AI services. This minimizes the chance of
nilerrors due to malformed AI prompts or model-specific input requirements, as the gateway can validate prompts against predefined structures before forwarding them to the LLM. - Performance Rivaling Nginx: A high-performance api gateway like APIPark can also handle high traffic loads gracefully. If a backend service is overwhelmed and starts returning malformed errors or
nilresponses due to internal pressure, APIPark can act as a buffer, applying rate limiting and circuit breakers to protect both the backend and the consuming applications from cascading failures that might otherwise lead tonilerrors.
By deploying an api gateway like APIPark, organizations can establish a robust front door for their services, ensuring consistency, reliability, and better error visibility, directly combating the ambiguity of "an error is expected but got nil."
6. Graceful Degradation and Fallbacks
For critical components, design for graceful degradation and implement fallback mechanisms.
- Circuit Breakers: Implement circuit breakers for calls to external services. If a service consistently returns errors (including implicitly
nilerrors), the circuit breaker can "trip," preventing further calls and allowing the system to use a fallback mechanism (e.g., cached data, default values) instead. This prevents repeated attempts to a failing service from generating morenilerrors. - Timeouts and Deadlines: Set strict timeouts for all external calls. If a response isn't received within the deadline, assume an error and return a specific timeout error, rather than allowing the call to hang indefinitely and potentially return
nilif the underlying connection drops. - Default Values: For non-critical data retrievals, if an operation fails (even with a
nilerror), consider returning well-defined default values instead of propagating the error ornil.
By combining defensive coding practices, strong error handling, rigorous validation, proactive testing, and strategic use of an advanced api gateway like APIPark, developers can significantly enhance the resilience of their applications and effectively mitigate the vexing problem of "an error is expected but got nil." This multi-layered approach transforms error handling from a reactive bug-fixing task into a proactive system design principle.
Deep Dive into Specific Keyword Contexts: Preventing nil in Complex Architectures
The error "an error is expected but got nil" takes on particular nuances and importance within the context of sophisticated architectural patterns like API Gateways, LLM Gateways, and Multi-Cloud Platforms (MCPs). These layers of abstraction and distributed environments introduce complexities that can either exacerbate or significantly mitigate the occurrence of such errors.
API Gateway & nil Errors: The Frontline Defender
An API gateway acts as the single entry point for a multitude of client requests, routing them to the appropriate backend services. Its role is not just about traffic management but also about enforcing policies, security, and crucially, standardizing communication, including error handling.
- Causes of
nilerrors originating from/through an API Gateway:- Backend Service Malfunctions: A common scenario is when a backend microservice fails internally but returns an unexpected, empty, or malformed response body instead of a proper error object (e.g., HTTP 500 with an empty JSON). If the API gateway is not configured to interpret such responses as explicit errors and transform them, it might simply pass on the ambiguous response. The downstream client, expecting a structured error from the gateway, might then encounter "an error is expected but got nil" when trying to parse the empty error payload.
- Gateway Transformation Errors: The API gateway itself might be configured to transform backend responses. If this transformation logic is flawed, it could mistakenly convert a valid backend error into a
nilor an unrecognizable format, especially if the transformation expects a specific input schema for errors that isn't met. - Gateway Internal Failures: Less common, but possible, is an internal failure within the API gateway itself (e.g., connection to a configuration service fails, or an internal plugin crashes). If the gateway's own error handling for such internal failures is not robust, it might return a generic
nilto the client instead of a specific gateway error. - Misconfigured Route/Policy: A misconfigured routing rule or a policy (e.g., authentication failure) within the gateway might prevent a request from reaching its intended backend, but instead of returning a clear 401/403, it might respond with an unhandled exception or
nilin an unexpected error field.
- How a robust API Gateway prevents
nilerrors:- Standardized Error Responses: A well-implemented API gateway can enforce a consistent error response format across all APIs it manages. Regardless of how a backend service fails, the gateway can intercept the raw error, transform it into a predefined, standardized JSON or XML error object, and return that to the client. This ensures that clients always receive a predictable error structure, eliminating the "expected error but got nil" because the error object is never
nilbut always a structured representation of the failure. - Schema Validation: Gateways can perform input and output schema validation. If a backend attempts to return an error response that doesn't conform to the defined error schema, the gateway can reject it or correct it before sending it to the client.
- Circuit Breaking and Retries: By implementing circuit breakers, the gateway can prevent calls to failing backend services, gracefully failing fast with a known error (e.g., "service unavailable") instead of allowing a potentially
nil-returning backend to be hit repeatedly. - Detailed Logging and Monitoring: As mentioned earlier, platforms like APIPark's comprehensive logging provide invaluable insights. If a
nilerror is suspected, the gateway's logs can reveal the exact raw response received from the backend, pinpointing if the backend is the source of thenilor if the issue lies in the gateway's transformation logic.
- Standardized Error Responses: A well-implemented API gateway can enforce a consistent error response format across all APIs it manages. Regardless of how a backend service fails, the gateway can intercept the raw error, transform it into a predefined, standardized JSON or XML error object, and return that to the client. This ensures that clients always receive a predictable error structure, eliminating the "expected error but got nil" because the error object is never
The api gateway acts as a critical choke point for error handling, offering an opportunity to normalize, enrich, and consistently present errors to consuming applications, thereby significantly reducing the prevalence of "an error is expected but got nil."
LLM Gateway & nil Errors: Navigating AI Uncertainty
The advent of Large Language Models (LLMs) and their integration into applications introduces a unique set of challenges, particularly concerning reliability and error handling. An LLM gateway serves a similar role to an API gateway but is specifically tailored for managing interactions with diverse AI models, whether hosted internally or by third-party providers.
- Causes of
nilerrors in LLM interactions:- Provider-Specific Failures: Different LLM providers (OpenAI, Google, Anthropic, custom models) have varied API error structures. A prompt engineering failure, token limit overrun, or model unavailability might result in a provider returning an error. If the LLM gateway or the application's direct client for a specific LLM doesn't correctly parse all possible error formats from all integrated providers, an unrecognized error might be treated as
nil. - Invalid Prompt/Input: If a prompt is too long, contains forbidden characters, or violates other model-specific constraints, the LLM might reject it. The rejection message from the LLM could be ambiguous, leading to
nilin the error field if the gateway's parsing logic isn't robust. - Rate Limiting/Quota Exhaustion: LLM providers impose strict rate limits. If exceeded, the response might be a generic 429 status code with a non-standard error body. An LLM gateway not prepared for this specific format might return
nilin the error position. - Internal Model Errors: Sometimes, the LLM itself might encounter an internal error during inference. The response could be truncated, malformed, or an empty JSON object, leading to
nilif the client expects a structured error.
- Provider-Specific Failures: Different LLM providers (OpenAI, Google, Anthropic, custom models) have varied API error structures. A prompt engineering failure, token limit overrun, or model unavailability might result in a provider returning an error. If the LLM gateway or the application's direct client for a specific LLM doesn't correctly parse all possible error formats from all integrated providers, an unrecognized error might be treated as
- How a robust LLM Gateway mitigates
nilerrors:- Unified Error Schema: A primary function of an LLM gateway should be to abstract away provider-specific error formats. It intercepts errors from various LLM APIs and transforms them into a consistent, internal error schema. This ensures that client applications always receive a predictable error object, regardless of the underlying LLM provider's error format, preventing
nilin the error field. - Intelligent Retries and Fallbacks: The gateway can implement intelligent retry logic for transient LLM errors (e.g., network issues, temporary provider outages). If retries fail, it can fall back to a different model or provider if configured, or return a standardized "LLM service unavailable" error rather than a
nilfor an internal failure. - Input Validation for Prompts: The LLM gateway can validate prompts against predefined rules (length, format, content) before forwarding them to the LLM. This pre-validation catches invalid inputs early, preventing potential
nilerrors that might arise from LLM rejections. - Rate Limiting and Quota Management: By centrally managing rate limits and quotas, the LLM gateway can prevent applications from exceeding them, returning clear "rate limit exceeded" errors rather than ambiguous
nilresponses from an overstressed LLM API. - Enhanced Observability: Like a general API gateway, an LLM gateway offers detailed logging of all interactions. This is crucial for debugging
nilerrors, allowing developers to see the exact request sent to and response received from the LLM, making it clear if theniloriginated from the LLM provider or the gateway's processing.
- Unified Error Schema: A primary function of an LLM gateway should be to abstract away provider-specific error formats. It intercepts errors from various LLM APIs and transforms them into a consistent, internal error schema. This ensures that client applications always receive a predictable error object, regardless of the underlying LLM provider's error format, preventing
An LLM gateway is a specialized form of API gateway designed to bring predictability and resilience to the inherently less predictable world of AI, significantly reducing nil errors stemming from diverse and often inconsistent LLM provider behaviors.
MCP (Multi-Cloud Platform) & nil Errors: Taming the Cloud Sprawl
A Multi-Cloud Platform (MCP) refers to an architecture where an organization utilizes services and infrastructure from multiple cloud providers (e.g., AWS, Azure, GCP, Alibaba Cloud) simultaneously, often for redundancy, cost optimization, or vendor lock-in avoidance. This distributed and heterogeneous environment amplifies the potential for "an error is expected but got nil" errors due to increased complexity and inconsistency.
- Causes of
nilerrors in an MCP:- Inconsistent Cloud SDKs and APIs: Each cloud provider has its own SDKs, APIs, and error conventions. A service deployed across multiple clouds might use different SDK versions or even entirely different libraries to access similar resources (e.g., storage, databases). If a resource access fails on one cloud, its SDK might return a concrete error, while on another, a different SDK might return
nilfor the error object in an unexpected scenario. - Configuration Drift: Managing configurations across different cloud providers can be challenging. A missing environment variable in one cloud, or a malformed secret in another, might lead a service to initialize with
nilconfiguration objects, eventually causing "an error is expected but got nil" when the service tries to use thosenilvalues. - Network Latency and Inter-Cloud Communication: Communication between services spanning different cloud regions or providers can experience variable latency and network issues. A service expecting an error object from a cross-cloud call might instead receive
nilif the connection drops silently or if a timeout is not handled consistently across different cloud networking layers. - Resource Provisioning Failures: Automated provisioning of resources (VMs, databases, queues) across multiple clouds requires robust error handling. If a provisioning script fails to create a resource in one cloud but doesn't return a clear error (e.g.,
nilwhere anErrResourceCreationFailedis expected), downstream services might attempt to use a non-existentnilresource. - Identity and Access Management (IAM) Complexities: IAM policies vary across clouds. A service might have permissions in one cloud but not another. If an access attempt fails due to permissions, and the cloud-specific client returns
nilinstead of a clear "access denied" error, it can lead to diagnostic nightmares.
- Inconsistent Cloud SDKs and APIs: Each cloud provider has its own SDKs, APIs, and error conventions. A service deployed across multiple clouds might use different SDK versions or even entirely different libraries to access similar resources (e.g., storage, databases). If a resource access fails on one cloud, its SDK might return a concrete error, while on another, a different SDK might return
- How to mitigate
nilerrors in an MCP:- Abstraction Layers: Implement a consistent abstraction layer (e.g., a custom library or framework) over cloud-specific SDKs. This layer should normalize inputs, outputs, and crucially, error responses across all integrated clouds. If a specific cloud SDK returns
nilfor an error, the abstraction layer should transform it into a standardized, non-nilerror object. - Centralized Configuration Management: Use a centralized configuration management system (e.g., Kubernetes ConfigMaps/Secrets, HashiCorp Consul/Vault, or a custom solution) that deploys and manages configurations consistently across all cloud environments. This prevents configuration drift and ensures that critical values are always present and correctly formatted, reducing
nil-related initialization errors. - Unified Observability: Implement a unified logging, tracing, and monitoring solution that spans all clouds within the MCP. This single pane of glass allows developers to trace requests and error propagation across different cloud boundaries, identifying exactly where a
nilerror originates in the multi-cloud journey. - Cloud-Agnostic Error Handling Policies: Define and enforce organization-wide error handling policies that dictate how services should behave and what kind of errors they should return, regardless of the underlying cloud provider. This includes mandating specific error codes, structured error payloads, and consistent logging.
- Automated Testing for Cross-Cloud Scenarios: Develop extensive integration tests that specifically target cross-cloud interactions, simulating failures in one cloud and verifying that services in other clouds handle them gracefully, returning proper errors instead of
nil.
- Abstraction Layers: Implement a consistent abstraction layer (e.g., a custom library or framework) over cloud-specific SDKs. This layer should normalize inputs, outputs, and crucially, error responses across all integrated clouds. If a specific cloud SDK returns
In an MCP environment, the principle of anticipating and standardizing errors becomes even more critical. By building robust abstraction layers and establishing consistent operational practices, organizations can manage the inherent complexity and prevent "an error is expected but got nil" from becoming a systemic issue across their diverse cloud deployments. The proactive management of these complex architectural components is not just about functionality, but about ensuring that when things go wrong, the system communicates those failures clearly, rather than with a confusing silence.
Practical Example: From Flawed to Flawless Error Handling
Let's illustrate how "an error is expected but got nil" can arise and how to fix it with a simplified, Go-like pseudocode example. Imagine a service that fetches user data, which sometimes might not exist, or the database might be unavailable.
Scenario 1: Flawed Implementation Leading to an error is expected but got nil
Consider a function findUserInDB that intends to find a user. The intention is: 1. If the user is found, return the user object and nil error. 2. If the user is not found, return nil user and nil error (this is the problematic part!). 3. If a database error occurs, return nil user and a concrete error.
// --- Problematic Code ---
package main
import (
"errors"
"fmt"
"log"
"time"
)
// User represents a user in our system
type User struct {
ID string
Name string
Email string
}
// simulateDB represents a mock database
var simulateDB = map[string]User{
"user123": {ID: "user123", Name: "Alice", Email: "alice@example.com"},
"user456": {ID: "user456", Name: "Bob", Email: "bob@example.com"},
}
// ErrDatabaseConnectionFailed is a custom error for DB connection issues
var ErrDatabaseConnectionFailed = errors.New("database connection failed")
// findUserInDB (Problematic Version)
// This function aims to find a user by ID.
// It has a bug where if user is not found, it returns (nil, nil) instead of (nil, ErrUserNotFound).
// Also simulates a database connection failure occasionally.
func findUserInDB(userID string) (*User, error) {
// Simulate occasional database connection failure
if time.Now().Second()%5 == 0 { // Fails every 5 seconds
return nil, ErrDatabaseConnectionFailed
}
// Simulate database lookup
user, found := simulateDB[userID]
if !found {
// !!! BUG HERE !!!
// If user is not found, we return nil for user and nil for error.
// A downstream caller expecting an error for "not found" will get nil.
return nil, nil // This is the source of the 'an error is expected but got nil' problem for "not found"
}
return &user, nil
}
// processUserRequest (Problematic Version)
// This function calls findUserInDB and assumes a non-nil error always means a DB issue.
// If user is not found, it tries to access user.Name on a nil user object.
func processUserRequest(userID string) {
log.Printf("Processing request for user ID: %s", userID)
user, err := findUserInDB(userID)
if err != nil {
// This block correctly handles actual database errors
log.Printf("Error finding user %s: %v", userID, err)
return
}
// !!! PROBLEM HERE !!!
// If findUserInDB returned (nil, nil) for "not found", 'err' is nil.
// We then proceed to dereference 'user' which is also nil.
// This will lead to a runtime panic: "runtime error: invalid memory address or nil pointer dereference"
// The debug message 'an error is expected but got nil' might appear if this code was within a test framework
// that specifically checks for error types, but in production, it's often a panic.
log.Printf("Found user: %s (ID: %s, Email: %s)", user.Name, user.ID, user.Email) // PANICS HERE if user is nil
}
func main() {
fmt.Println("--- Running Problematic Code ---")
// Test cases
processUserRequest("user123") // Should succeed
processUserRequest("nonexistent") // Will cause a panic (runtime error) if user is not found
processUserRequest("user456") // Should succeed
time.Sleep(1 * time.Second) // Wait for a second for the DB error simulation
processUserRequest("user789") // Might cause DB connection error or panic for nonexistent
fmt.Println("\nWait for a few seconds to potentially hit the DB connection failure simulation...")
time.Sleep(3 * time.Second) // Wait for a second for the DB error simulation
processUserRequest("user999") // Might cause DB connection error
fmt.Println("--- End of Problematic Code ---")
}
Explanation of the Problem:
In findUserInDB, when !found is true (user not in simulateDB), it returns (nil, nil). The processUserRequest function then correctly checks if err != nil, which evaluates to false because err is nil. It then proceeds to log.Printf("Found user: %s ...", user.Name...). At this point, user is nil, leading to a runtime panic: "runtime error: invalid memory address or nil pointer dereference."
If this processUserRequest was embedded within a test harness or a framework that explicitly asserts that if a resource isn't found, a specific ErrNotFound must be returned, then the test framework would likely output "an error is expected but got nil" because it expected ErrNotFound but received nil in the error slot.
Scenario 2: Corrected Implementation with Robust Error Handling
To fix this, we need to explicitly return a distinct error when a user is not found.
// --- Corrected Code ---
package main
import (
"errors"
"fmt"
"log"
"time"
)
// User represents a user in our system
type User struct {
ID string
Name string
Email string
}
// simulateDB represents a mock database
var simulateDB = map[string]User{
"user123": {ID: "user123", Name: "Alice", Email: "alice@example.com"},
"user456": {ID: "user456", Name: "Bob", Email: "bob@example.com"},
}
// ErrDatabaseConnectionFailed is a custom error for DB connection issues
var ErrDatabaseConnectionFailed = errors.New("database connection failed")
// ErrUserNotFound is a custom error for when a user cannot be found
var ErrUserNotFound = errors.New("user not found")
// findUserInDB (Corrected Version)
// This function finds a user by ID. It now returns ErrUserNotFound when user is not found.
func findUserInDB(userID string) (*User, error) {
// Simulate occasional database connection failure
if time.Now().Second()%5 == 0 { // Fails every 5 seconds
return nil, ErrDatabaseConnectionFailed
}
// Simulate database lookup
user, found := simulateDB[userID]
if !found {
// Corrected: Return a specific error for "not found"
return nil, ErrUserNotFound
}
return &user, nil
}
// processUserRequest (Corrected Version)
// This function correctly handles both database errors and "user not found" scenarios.
func processUserRequest(userID string) {
log.Printf("Processing request for user ID: %s", userID)
user, err := findUserInDB(userID)
if err != nil {
// Now we can distinguish between different types of errors
if errors.Is(err, ErrUserNotFound) {
log.Printf("User %s not found. Taking appropriate action (e.g., redirect to signup).", userID)
} else if errors.Is(err, ErrDatabaseConnectionFailed) {
log.Printf("Database error while finding user %s: %v. Please try again later.", userID, err)
} else {
log.Printf("An unexpected error occurred for user %s: %v", userID, err)
}
return
}
// Only if err is nil AND user is not nil, proceed with user data
log.Printf("Found user: %s (ID: %s, Email: %s)", user.Name, user.ID, user.Email)
}
func main() {
fmt.Println("--- Running Corrected Code ---")
// Test cases
processUserRequest("user123") // Should succeed
processUserRequest("nonexistent") // Now correctly handles "user not found"
processUserRequest("user456") // Should succeed
time.Sleep(1 * time.Second) // Wait for a second for the DB error simulation
processUserRequest("user789") // Might cause DB connection error or correctly handle "user not found"
fmt.Println("\nWait for a few seconds to potentially hit the DB connection failure simulation...")
time.Sleep(3 * time.Second) // Wait for a second for the DB error simulation
processUserRequest("user999") // Might cause DB connection error
fmt.Println("--- End of Corrected Code ---")
}
Key Improvements:
- Explicit
ErrUserNotFound: ThefindUserInDBfunction now returnsErrUserNotFoundwhen a user is not found, instead of(nil, nil). This adheres to the principle that a logical failure (like not finding a resource) should still be signaled with a specific error object, not just by anilvalue. - Discriminating Error Handling: The
processUserRequestfunction now useserrors.Is(Go's standard way to check for specific error types) to differentiate betweenErrUserNotFoundandErrDatabaseConnectionFailed. This allows for more precise and appropriate actions based on the specific type of error. - No
nilDereference: Becauseuseris only accessed iferrisniland auserwas actually found, thelog.Printfline will no longer panic. The code is now defensively programmed againstnilpointers.
This practical example vividly demonstrates how a subtle oversight in returning nil where a specific error is expected can lead to runtime crashes or, in a more controlled test environment, the precise message "an error is expected but got nil." The fix involves rigorously adhering to error handling contracts and ensuring that all failure conditions, both technical and logical, are communicated via explicit, non-nil error objects.
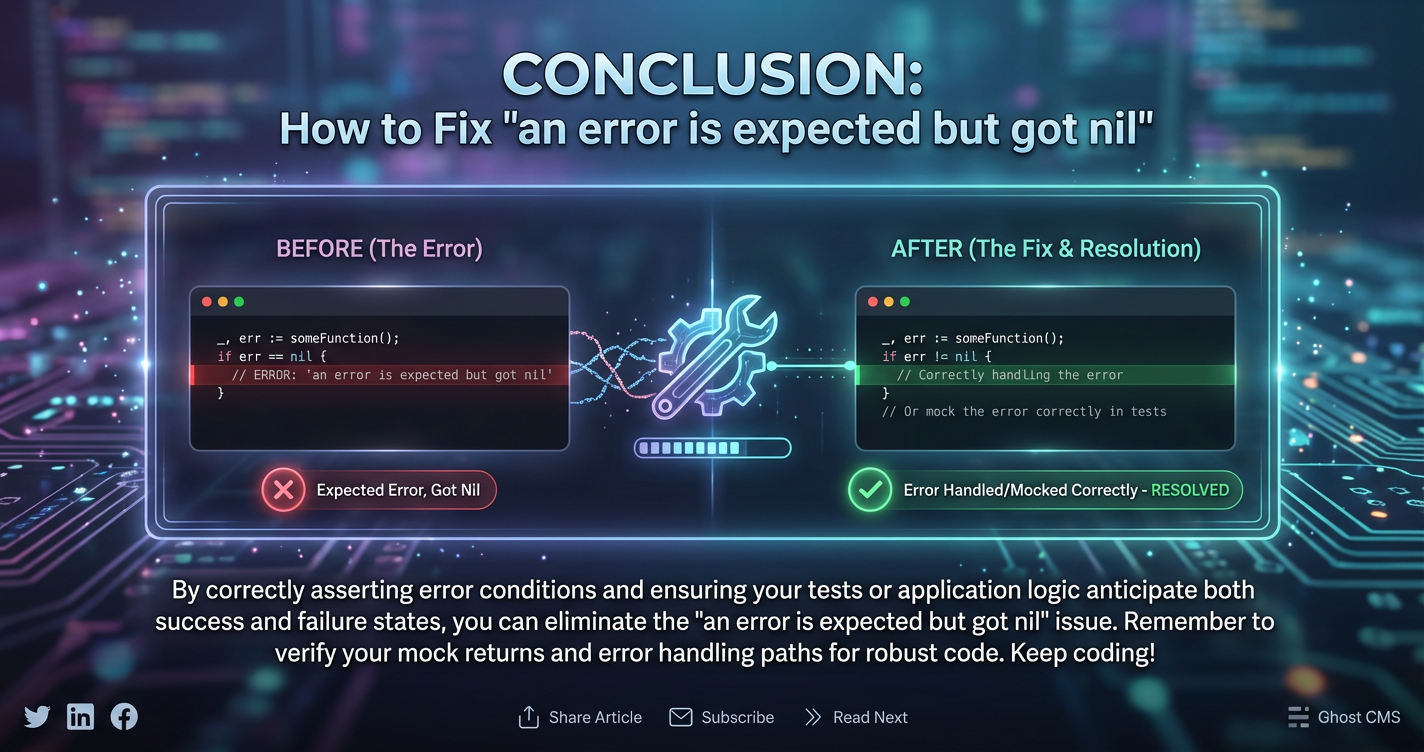
Conclusion: Mastering the Art of Error Resilience
The error message "an error is expected but got nil" is far more than a cryptic bug; it's a profound indicator of a critical gap in a system's error handling philosophy. It speaks to a fundamental breakdown in the contract between different parts of an application, where the expected signal of failure—a concrete error object—is replaced by an ambiguous void. Left unaddressed, these silent failures can propagate through complex distributed architectures, leading to data inconsistencies, service disruptions, and considerable developer frustration.
Our comprehensive exploration has illuminated the multifaceted origins of this error, from misconfigured API calls and database operations to the nuanced challenges of concurrency and the intricacies of multi-cloud environments. We've seen how external dependencies, including the diverse behaviors of Large Language Models, can introduce unexpected nil values if not managed rigorously. Crucially, we've outlined a systematic approach to diagnosis, emphasizing the power of diligent code review, robust logging and tracing, interactive debugging, and proactive testing.
The path to resolving and preventing "an error is expected but got nil" is paved with best practices rooted in defensive programming: the unwavering commitment to always checking for nil where a value might be absent, the implementation of explicit and context-rich error objects, and the consistent validation of inputs at every boundary. Furthermore, leveraging modern architectural components like an api gateway and an llm gateway provides invaluable layers of abstraction, allowing for the standardization of error formats, intelligent traffic management, and enhanced observability—features that directly combat the ambiguity of nil errors by ensuring that all failures are clearly articulated. Solutions like APIPark, with its comprehensive API lifecycle management, unified AI invocation, and detailed logging capabilities, exemplify how strategic tooling can transform error handling from a reactive burden into a proactive strength.
Ultimately, mastering the art of error resilience is not about eliminating all errors—an impossible feat in any complex system. Instead, it's about transforming errors from silent, destructive forces into loud, informative signals that guide diagnosis and enable graceful recovery. By understanding the true meaning of nil in error contexts, embracing a proactive mindset, and deploying the right tools and architectural patterns, developers can build applications that are not only functional but also inherently robust, reliable, and capable of navigating the unpredictable landscape of modern software. The journey from "expected error but got nil" to a system that always provides a clear answer is a testament to meticulous engineering and a commitment to operational excellence.
Frequently Asked Questions (FAQs)
1. What does "an error is expected but got nil" fundamentally mean?
This error message indicates a mismatch between what the code expects (a non-nil object representing an error) and what it actually receives (a nil value in the error position). It means that a logical or technical failure likely occurred, but the mechanism responsible for generating a detailed error object either failed or returned an empty value (nil), leaving the calling code in a state of confusion where it was prepared to handle an error, but received none. It's often a symptom of an incomplete error reporting path or a bug in a function that should return an error on failure but mistakenly returns nil.
2. How does an API Gateway help prevent this specific error?
An API gateway acts as a centralized control point for all API traffic. It can prevent "an error is expected but got nil" by: 1. Standardizing Error Responses: Intercepting ambiguous or malformed error responses from backend services and transforming them into a consistent, well-defined error format that clients expect. 2. Enforcing Schemas: Validating request and response bodies against predefined schemas, ensuring that error payloads adhere to a consistent structure. 3. Circuit Breaking: Rapidly failing (with a known error) when backend services are unhealthy, rather than allowing clients to hit a failing service that might return nil or unexpected responses. 4. Detailed Logging: Providing granular logs of all API interactions, which helps in diagnosing whether the nil originated from the backend or the gateway itself.
3. What role does an LLM Gateway play in mitigating nil errors when interacting with AI models?
An LLM gateway is specialized to manage interactions with various Large Language Models (LLMs). It mitigates nil errors by: 1. Unifying Error Formats: Abstracting away the diverse and often inconsistent error structures of different LLM providers, ensuring client applications always receive a standardized, non-nil error object. 2. Intelligent Retries and Fallbacks: Handling transient LLM failures with smart retries or falling back to alternative models, returning a consistent error if all attempts fail, rather than an ambiguous nil. 3. Prompt Validation: Validating incoming prompts against LLM-specific constraints to prevent rejections that might otherwise result in unclear or nil error responses from the model. 4. Rate Limit Management: Centrally managing LLM rate limits and returning clear "rate limit exceeded" errors before the underlying LLM API is hit, preventing vague nil responses due to over-usage.
4. Are there specific challenges with "expected error but got nil" in Multi-Cloud Platform (MCP) environments?
Yes, MCP environments inherently increase the complexity and potential for this error due to: 1. Inconsistent Cloud SDKs: Different cloud providers have varying SDKs and API error conventions; an error in one cloud might be clearly defined, while in another, a similar failure could result in nil. 2. Configuration Drift: Managing configurations across multiple clouds can lead to missing or malformed values, causing services to initialize with nil objects. 3. Inter-Cloud Communication Issues: Network failures or timeouts between different cloud regions/providers might lead to nil returns if not handled consistently by cross-cloud communication layers. Mitigation involves abstraction layers, centralized configuration, and unified observability across all clouds.
5. What are the immediate steps I should take if I encounter "an error is expected but got nil" in my application?
- Locate the Exact Origin: Pinpoint the exact line of code where the error message appears in your logs or debugger.
- Trace Back the Error Variable: Meticulously trace the variable that received
nilin the error position back through the call stack to identify where it was last assigned or where a function returned(value, nil)when it should have returned(value, error). - Review Function Contracts: Examine the function that returned the
nilerror. Does it always explicitly return a non-nilerror object for all failure paths? Are there any conditional branches that might return(nil, nil)unintentionally? - Enhance Logging: Temporarily add detailed log statements before and after the problematic function call, logging the exact values returned for both the result and the error, to pinpoint the source of the
nil. - Utilize Debugger: Step through the code execution with an IDE debugger to inspect variable states in real-time and observe the moment the error variable becomes
nil.
🚀You can securely and efficiently call the OpenAI API on APIPark in just two steps:
Step 1: Deploy the APIPark AI gateway in 5 minutes.
APIPark is developed based on Golang, offering strong product performance and low development and maintenance costs. You can deploy APIPark with a single command line.
curl -sSO https://download.apipark.com/install/quick-start.sh; bash quick-start.sh

In my experience, you can see the successful deployment interface within 5 to 10 minutes. Then, you can log in to APIPark using your account.

Step 2: Call the OpenAI API.