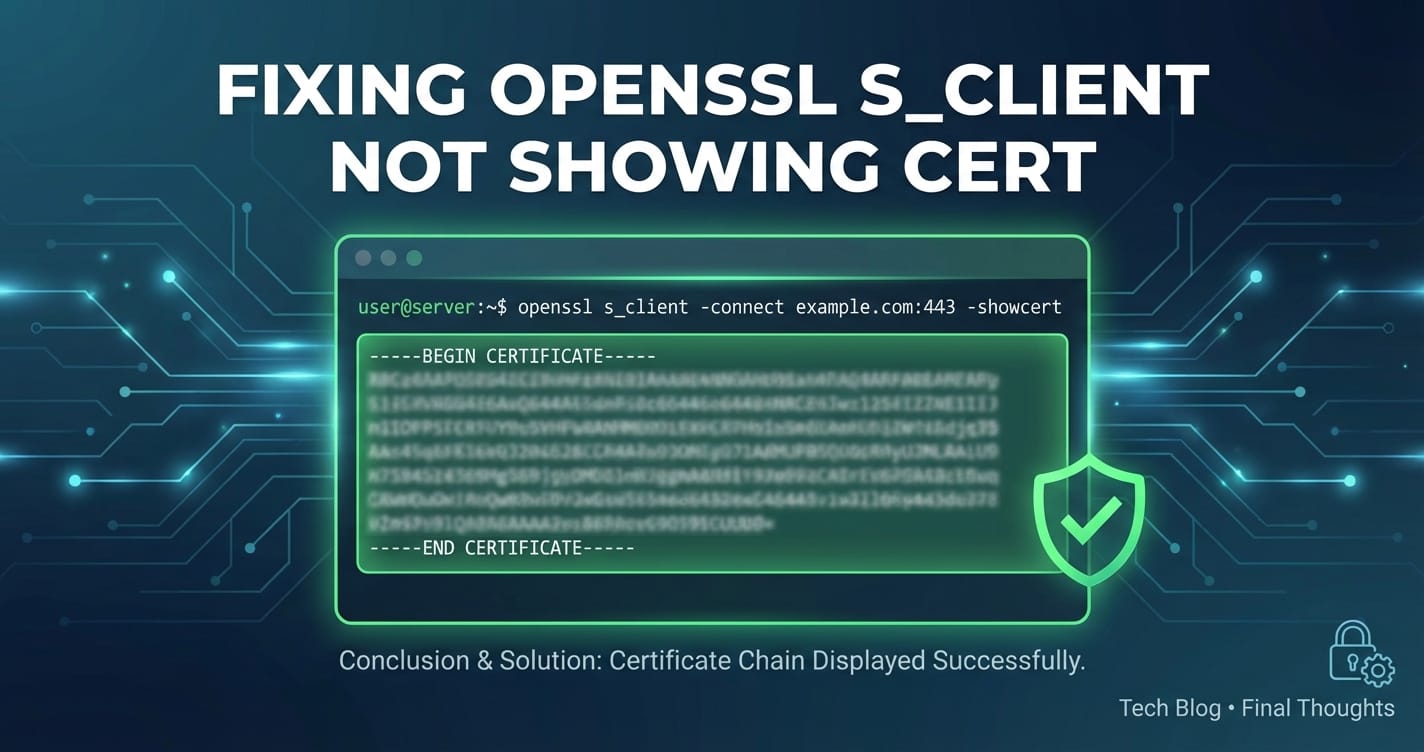
Fixing openssl s_client Not Showing Cert with -showcert
In the complex landscape of network security and service communication, openssl s_client stands as an indispensable tool for diagnosing TLS/SSL connectivity issues. For developers, system administrators, and security professionals, it’s the go-to utility for peering into the secure handshake process, verifying server certificates, and troubleshooting encrypted communication channels. However, a common point of frustration arises when running openssl s_client -showcert seemingly fails to display the expected server certificate, or only shows a partial chain. This article delves deep into the intricacies of openssl s_client, exploring the underlying mechanisms of TLS, identifying the multifarious reasons why -showcert might not behave as anticipated, and providing comprehensive, actionable strategies to diagnose and resolve these elusive issues. We will journey through common pitfalls, advanced debugging techniques, and best practices, ensuring you can confidently pinpoint and rectify certificate display anomalies, thereby securing your api endpoints and api gateway deployments.
The importance of verifying server certificates cannot be overstated. In an era where man-in-the-middle attacks and sophisticated phishing schemes are rampant, ensuring that your client is communicating with the legitimate server, and not an impostor, is paramount. openssl s_client is often the first line of defense in confirming this trust. When it fails to present the certificate chain clearly, it leaves a critical blind spot, potentially masking misconfigurations, network interferences, or even malicious interceptions. Understanding the nuances of this command is not just about debugging; it's about upholding the integrity of your secure communications.
The Core Functionality of openssl s_client: A Primer on TLS/SSL Handshake
Before we dissect the problem, it's crucial to solidify our understanding of what openssl s_client is designed to do and how the TLS/SSL handshake operates. At its heart, openssl s_client simulates an SSL/TLS client connecting to a remote host and port. Its primary purpose is to establish a secure, encrypted connection and then, optionally, to display various details about that connection, including the server's certificate.
The TLS (Transport Layer Security) protocol, the successor to SSL, is a cryptographic protocol designed to provide communication security over a computer network. When a client (like your browser, an application, or openssl s_client) attempts to connect to a server securely, a series of steps, known as the TLS handshake, unfolds:
- Client Hello: The client initiates the connection by sending a "Client Hello" message. This message includes the TLS versions it supports, a list of cipher suites it's willing to use, and a random byte string known as the "client random." Crucially, it also includes the server name it's trying to connect to (Server Name Indication, or SNI), especially important for servers hosting multiple domains on the same IP address.
- Server Hello: The server responds with a "Server Hello." It selects the highest TLS version and the strongest cipher suite supported by both parties from the client's list. It also provides its own "server random" byte string.
- Certificate: The server sends its digital certificate to the client. This certificate contains the server's public key, its identity (domain name), the issuer's identity, and a digital signature from a Certificate Authority (CA) that attests to the certificate's authenticity. Often, the server also sends a chain of intermediate CA certificates leading up to a trusted root CA.
- Server Key Exchange (Optional): If the chosen cipher suite requires it, the server may send a Server Key Exchange message.
- Server Hello Done: The server signals that it has finished its part of the initial handshake.
- Client Certificate (Optional): If the server requests client authentication, the client sends its own certificate.
- Client Key Exchange: The client generates a pre-master secret, encrypts it with the server's public key (obtained from the server's certificate), and sends it to the server.
- Change Cipher Spec: Both client and server then switch to using the newly negotiated cipher suite and the derived session keys for encryption.
- Finished: Both parties send "Finished" messages, encrypted with the new keys. These messages are hashes of all previous handshake messages, verifying that the handshake was not tampered with.
Once these steps are successfully completed, an encrypted channel is established, and application data can be securely exchanged. openssl s_client allows us to observe and interact with each of these phases, providing unparalleled insight into the secure connection process.
The openssl s_client command offers a plethora of options to fine-tune its behavior and output. For instance, -connect host:port specifies the target, -servername hostname explicitly sets the SNI, and crucially for our discussion, -showcert is intended to display the entire certificate chain sent by the server. When this command executes, it performs the client-side of the TLS handshake, attempting to validate the server's certificate against its local trust store (or a specified CA file/path). If the handshake is successful and the certificate chain can be built and verified, the details are typically printed to standard output. However, the -showcert option, despite its name, has a specific function: it tells OpenSSL to dump all certificates received from the server, regardless of whether they could be successfully verified or chain to a trusted root. This distinction is critical and often misunderstood, leading to confusion when troubleshooting.
Unpacking the -showcert Conundrum: Why It Might Not Show What You Expect
The expectation with openssl s_client -showcert is often that it will reveal the complete, validated certificate chain. When it doesn't, or when it shows an incomplete chain, it's indicative of a deeper issue. The reasons can range from simple client-side misconfigurations to complex server-side problems or even insidious network interferences. Let's systematically break down the most common scenarios.
1. Server Name Indication (SNI) Issues
One of the most frequent culprits behind incomplete or incorrect certificate displays is an SNI mismatch. SNI is an extension to the TLS protocol that allows a client to indicate which hostname it is trying to connect to at the start of the handshake process. This is particularly important for servers that host multiple websites (virtual hosts) on a single IP address, each with its own TLS certificate.
If you connect to an IP address directly or omit the -servername flag, the server might present its default certificate, which may not be the one associated with the domain you intend to test. For example, if a server hosts both example.com and api.example.com, and you connect to api.example.com's IP without specifying -servername api.example.com, the server might send the certificate for example.com or a wildcard certificate, or even no specific certificate if it's not configured to handle non-SNI requests gracefully for that virtual host.
How to Identify and Fix: Always use the -servername flag when connecting to a hostname that is served by a virtual host. Ensure the value passed to -servername exactly matches the hostname you are connecting to.
# Incorrect or incomplete (may show default cert or fail)
openssl s_client -showcert -connect api.example.com:443
# Correct approach with SNI
openssl s_client -showcert -servername api.example.com -connect api.example.com:443
Without the correct SNI, the server doesn't know which certificate to present, leading to the display of an irrelevant certificate or potentially a handshake failure if the server is strictly configured. This is a critical point when debugging api endpoints, as many api gateway services leverage virtual hosting extensively.
2. Missing Intermediate Certificates / Incomplete Server Chain
A TLS certificate is typically part of a chain of trust. At the top is a Root Certificate Authority (CA) certificate, which is self-signed and pre-installed in operating systems and browsers. Below the root are one or more Intermediate CA certificates, which are signed by the root CA or another intermediate CA. Finally, at the bottom is the server's end-entity certificate, signed by an intermediate CA. For a client to trust the server's certificate, it must be able to build a complete chain from the server's certificate all the way up to a trusted root CA.
A common server misconfiguration is sending only the end-entity certificate, or only a partial chain, failing to include all necessary intermediate certificates. When openssl s_client receives an incomplete chain, it might still display what it received with -showcert, but it will then report a verification error (e.g., unable to get local issuer certificate or self signed certificate in certificate chain). The key here is that -showcert will show what the server sent, but the verification output will tell you if the chain is incomplete or untrusted.
How to Identify and Fix: * Verification Errors: Look for verification errors in the openssl s_client output, specifically related to unable to get local issuer certificate or self signed certificate in certificate chain. * Manual Chain Inspection: Examine the certificates displayed by -showcert. Check the Issuer field of each certificate and compare it with the Subject field of the next certificate in the chain (working upwards). If there's a gap before a known root CA, then intermediate certificates are missing. * Server Configuration: The server administrator needs to concatenate the server's certificate with all intermediate CA certificates into a single file and configure the web server (e.g., Nginx, Apache, or a gateway like APIPark) to send this complete bundle. The order is crucial: server cert first, followed by intermediates, up to but usually not including the root.
Example of a missing intermediate:
---
Certificate chain
0 s:/CN=api.example.com
i:/C=US/O=Let's Encrypt/CN=R3
1 s:/C=US/O=Internet Security Research Group/CN=R3
i:/C=US/O=Internet Security Research Group/CN=ISRG Root X1
---
Verify return code: 21 (unable to get local issuer certificate)
In this output, certificate 0 is signed by R3. Certificate 1 is R3 itself, signed by ISRG Root X1. If your client doesn't directly trust ISRG Root X1, and the server didn't send ISRG Root X1 (which is typically trusted by default), then the chain might still be incomplete if another intermediate was expected. The most common scenario is where ISRG Root X1 is not sent, and the client needs it, or an older DST Root CA X3 (which expired). The important takeaway is to ensure the server sends all intermediates necessary for the client to build a path to a trusted root.
3. Untrusted Root CA / Local Trust Store Issues
Even if the server sends a complete certificate chain, openssl s_client might still report verification errors if the client's system does not trust the ultimate root CA in that chain. This often happens with custom or enterprise CAs that are not part of the standard OS/browser trust stores.
How to Identify and Fix: * Verification Errors: Look for unable to get local issuer certificate or self signed certificate in certificate chain errors again, even if all intermediates seem present. This often means the root CA is unknown. * Specify Trust Store: You can explicitly tell openssl s_client where to find trusted root certificates using -CAfile (for a single file containing concatenated trusted CAs) or -CApath (for a directory containing trusted CAs, hashed appropriately).
# Trusting a custom CA bundle
openssl s_client -showcert -servername api.example.com -connect api.example.com:443 -CAfile /etc/ssl/certs/my_custom_ca_bundle.pem
For api development in internal networks, this is a common necessity, especially when dealing with self-signed certificates or internal PKI solutions.
4. Network Proxies or Interceptors (Man-in-the-Middle)
Enterprise network environments, security software, or even malware can sometimes intercept TLS connections, acting as a man-in-the-middle (MITM) proxy. In such scenarios, the proxy terminates the client's TLS connection, establishes its own connection to the target server, and then re-encrypts the traffic between itself and the client using a dynamically generated certificate, often signed by an internal CA.
When openssl s_client connects through such a proxy, it will display the proxy's certificate, not the actual server's certificate. The proxy's certificate will likely be signed by a CA that is either explicitly trusted by your system (if it's an enterprise proxy) or, if not, will result in a verification error. The -showcert output will accurately reflect what the proxy sent, which is not the server's original certificate.
How to Identify and Fix: * Unexpected Issuer: If -showcert shows a certificate issued by an entity other than the expected CA (e.g., issued by "Your Company Proxy CA" instead of "Let's Encrypt" or "DigiCert"), you're likely behind an MITM proxy. * Proxy Configuration: Configure openssl to use the proxy (if it's an HTTP/S proxy) via environment variables or specific OpenSSL proxy options, although s_client itself doesn't directly support HTTP proxies without CONNECT method. For direct TLS interception, you need to be aware of your network environment. * Trusting the Proxy CA: If the proxy's CA is legitimate for your environment, ensure its certificate is added to your client's trust store (e.g., via -CAfile). * Bypass Proxy (if possible): If you need to see the actual server certificate, you might need to test from a network location that does not intercept TLS traffic.
This situation can be particularly tricky when debugging external api calls or connecting to a public api gateway from an internal, tightly controlled network.
5. Server Misconfiguration (Not Sending Certificate)
While rare for standard web servers, it's theoretically possible for a server to be misconfigured to not send a certificate at all during the handshake, or to send an empty certificate message. In such cases, openssl s_client -showcert would naturally show nothing because nothing was received. This would almost always result in a fatal handshake error (no shared cipher, handshake failure), indicating a fundamental problem on the server side.
How to Identify and Fix: If openssl s_client consistently fails with handshake errors and showcert yields no output, verify the server's TLS configuration. Ensure a certificate and private key are correctly configured and loaded.
6. Firewall or Network Issues
Firewalls or network devices in the path might interfere with the TLS handshake. While less common to specifically prevent certificate display while allowing the connection to establish, a firewall could potentially prune parts of the handshake, although this usually results in a complete connection failure. More likely, a firewall could prevent specific TLS versions or cipher suites from being negotiated, leading to handshake failures.
How to Identify and Fix: * Network Diagnostics: Use ping, traceroute/tracert to check basic connectivity and path. * Port Check: Use nc -vz host port or telnet host port to verify that the port is open and reachable. * TLS Version/Cipher Check: Try forcing specific TLS versions (-tls1_2, -tls1_3) or cipher suites (-ciphers) with openssl s_client to see if a specific version or cipher is being blocked or causing issues.
# Force TLSv1.2
openssl s_client -showcert -servername api.example.com -connect api.example.com:443 -tls1_2
7. TLS Version Incompatibility
Modern TLS clients and servers negotiate the highest common TLS version they both support. If a server only supports older, deprecated versions (e.g., TLS 1.0 or 1.1) and your openssl client is configured to only prefer newer ones, or vice-versa, a handshake failure can occur, or the server might behave unexpectedly. Some legacy servers might also have issues with modern TLS 1.3 features. When a handshake fails due to version incompatibility, no certificate will be successfully transmitted or displayed.
How to Identify and Fix: * Experiment with Versions: Use options like -tls1_2, -tls1_3, -ssl3, -tls1, -tls1_1 (though ssl3 and tls1 are deprecated and insecure) to manually force openssl s_client to attempt different TLS versions. * Server Logs: Check the server's TLS error logs for negotiation failures.
8. Client Certificate Authentication (if applicable)
In some specialized scenarios, particularly for internal api services or highly secure gateway environments, the server might require the client to present its own certificate for mutual (two-way) TLS authentication. If the server requests a client certificate and the client (openssl s_client) does not provide one (or provides an invalid one), the handshake will fail, and the server's certificate may not be fully processed or displayed.
How to Identify and Fix: * Handshake Failure: Look for errors indicating no client certificate received or bad certificate during client authentication. * Provide Client Certificate: Use -cert and -key options to provide the client's certificate and private key to openssl s_client:
openssl s_client -showcert -servername api.example.com -connect api.example.com:443 -cert client.crt -key client.key -CAfile server_ca_bundle.pem
This is a more advanced use case, often seen in service-to-service communication behind a robust api gateway.
9. Incorrect Hostname or IP Address
A simple yet often overlooked issue is an incorrect hostname or IP address in the -connect parameter. If you're connecting to the wrong host, you will naturally get the wrong certificate (or no connection at all). This can happen due to DNS resolution issues, typos, or stale cache entries.
How to Identify and Fix: * Verify DNS: Use dig or nslookup to ensure the hostname resolves to the correct IP address. * Double-Check Configuration: Re-verify the hostname and port in your command. * Check hosts file: Ensure there are no overriding entries in your local /etc/hosts file (or C:\Windows\System32\drivers\etc\hosts on Windows).
Advanced Debugging with openssl s_client: Peering Deeper
When -showcert isn't enough, OpenSSL provides more verbose options to truly understand the handshake process.
-debug, -msg, -state, -trace
-debug: This option prints diagnostic debugging information, including raw bytes of the TLS records. It's extremely verbose and useful for understanding the exact data being exchanged.-msg: Shows all protocol messages that are exchanged, without the raw byte dump. This is often more human-readable than-debugfor analyzing the handshake flow.-state: Prints the SSL engine state changes. This gives you a clear indication of which part of the handshake is being processed.-trace: (Newer OpenSSL versions) Similar to-msg, but can offer even more granular detail.
Combining these flags can provide a comprehensive view of the handshake, helping to pinpoint exactly where the certificate exchange is failing or being truncated.
# Example with verbose debugging
openssl s_client -showcert -servername api.example.com -connect api.example.com:443 -msg -state -debug
Analyzing the output requires a good understanding of the TLS protocol specification, but even without deep expertise, you can often spot anomalies like unexpected messages, repeated messages, or an abrupt termination of the handshake.
Interpreting Verbose Output
When using -msg or -debug, look for the Certificate message from the server. This is where the server transmits its certificate chain. If this message is missing, malformed, or contains fewer certificates than expected, that's your clue.
Certificatemessage: Indicates the server is sending certificates.Server Hello Done: Means the server has finished its initial response. If this appears before aCertificatemessage (and client certs aren't expected), something is wrong.Alertmessages: These are critical.Alert fatal: handshake failure,Alert warning: close notifyetc., immediately tell you where the connection broke down.
Practical Troubleshooting Walkthroughs
Let's illustrate with a couple of common scenarios.
Scenario 1: Debugging an api Endpoint with SNI Issues
Imagine you're developing an application that connects to myapi.example.com. Your application works in production, but from your dev machine, openssl s_client is failing to show the correct certificate or giving verification errors.
Initial Attempt:
openssl s_client -showcert -connect myapi.example.com:443
Output Observation: You see a certificate, but its Subject is CN=default-host.example.com, not myapi.example.com. And there's a verification error Verify return code: 62 (Hostname mismatch). The -showcert option did show a certificate, but it's the wrong one.
Diagnosis: The server is likely hosting multiple domains on the same IP address and is sending its default certificate because no SNI was provided. openssl s_client implicitly tried to use the hostname from -connect for SNI, but perhaps there's an internal DNS resolution issue or the server is configured oddly.
Solution: Explicitly provide the SNI.
openssl s_client -showcert -servername myapi.example.com -connect myapi.example.com:443
Expected Output: Now, the certificate Subject should be CN=myapi.example.com, and the Verify return code should be 0 (ok) (assuming the chain is complete and trusted).
This scenario highlights why -showcert can be misleading if not interpreted alongside other output and an understanding of SNI. The certificate was shown, but it wasn't the expected one due to an SNI oversight.
Scenario 2: Missing Intermediate Certificates on an api gateway
You've deployed a new api gateway instance, let's call it gateway.example.com, and configured it with a Let's Encrypt certificate. When you test it with openssl s_client, you get verification errors.
Initial Attempt:
openssl s_client -showcert -servername gateway.example.com -connect gateway.example.com:443
Output Observation:
---
Certificate chain
0 s:/CN=gateway.example.com
i:/C=US/O=Let's Encrypt/CN=R3
---
Verify return code: 21 (unable to get local issuer certificate)
The -showcert option only shows one certificate: the server's end-entity certificate. It's issued by R3. The verification error unable to get local issuer certificate strongly suggests that the intermediate certificate (R3, signed by ISRG Root X1) was not sent by the server, and openssl couldn't find it in its default trust store to complete the chain to a trusted root.
Diagnosis: The api gateway is misconfigured to send only the end-entity certificate, missing the intermediate certificate(s) required to establish a full chain of trust to a widely recognized root CA.
Solution: The gateway administrator needs to correct the certificate configuration. For Let's Encrypt, this typically means using the fullchain.pem file instead of cert.pem for the server's certificate setting. The fullchain.pem bundles the server certificate and all necessary intermediate certificates.
After the server configuration is updated and the gateway is restarted:
openssl s_client -showcert -servername gateway.example.com -connect gateway.example.com:443
Expected Output:
---
Certificate chain
0 s:/CN=gateway.example.com
i:/C=US/O=Let's Encrypt/CN=R3
1 s:/C=US/O=Internet Security Research Group/CN=R3
i:/C=US/O=Internet Security Research Group/CN=ISRG Root X1
---
Verify return code: 0 (ok)
Now, two certificates are shown, forming a complete chain to the ISRG Root X1 (which is typically trusted by default), and the verification is successful. This demonstrates that -showcert accurately reflects what the server sends, and the verification step tells you if that chain is valid.
APIPark is a high-performance AI gateway that allows you to securely access the most comprehensive LLM APIs globally on the APIPark platform, including OpenAI, Anthropic, Mistral, Llama2, Google Gemini, and more.Try APIPark now! 👇👇👇
The Role of api gateway in Certificate Management and Connection Security
The discussion around openssl s_client often revolves around point-to-point connections. However, in modern microservices architectures and api ecosystems, an api gateway plays a pivotal role in abstracting, securing, and routing traffic to backend services. A robust api gateway often terminates TLS connections from clients, manages certificates, and then establishes new, secure connections to upstream services. This makes api gateway a critical component for certificate lifecycle management.
Debugging certificate issues when an api gateway is involved adds another layer of complexity. If openssl s_client is failing against an api gateway endpoint, the problem could be:
- Client-to-Gateway: The
api gatewayitself is misconfigured to present an incorrect, incomplete, or expired certificate. This is the scenario we've been largely discussing. - Gateway-to-Upstream: The
api gatewayis failing to establish a secure connection to a backendapiservice due to certificate issues on the upstream side.openssl s_clientwould typically not reveal this directly, as it only tests the client-to-gateway connection. However, gateway logs would indicate upstream TLS errors.
Effective api gateway solutions incorporate features for centralized certificate management, automated renewal (e.g., integration with ACME providers like Let's Encrypt), and robust TLS configuration options. These features significantly reduce the manual effort and error proneness associated with certificate handling, which in turn minimizes the likelihood of encountering the -showcert conundrum.
For organizations managing a multitude of APIs, especially those leveraging AI models or complex microservices architectures, the operational overhead of securing each endpoint manually becomes unsustainable. This is where comprehensive api gateway and management platforms like ApiPark become invaluable. APIPark, as an open-source AI gateway and API developer portal, centralizes the management of TLS certificates across all integrated APIs. It simplifies the secure deployment of AI and REST services by providing unified authentication, cost tracking, and crucially, end-to-end API lifecycle management, which inherently includes robust certificate handling. By consolidating prompt encapsulation into REST APIs, managing traffic, load balancing, and versioning, APIPark ensures that the underlying TLS configurations are correctly applied and maintained, reducing the need for extensive manual openssl s_client debugging on client-facing endpoints. With features like quick integration of 100+ AI models and performance rivaling Nginx, APIPark addresses the challenges of both securing and scaling api infrastructure, making certificate issues less frequent and more manageable.
Best Practices for Certificate Management
To minimize the instances where openssl s_client -showcert gives you headaches, adopt these best practices:
- Automate Certificate Renewal: Implement automated solutions (e.g., Let's Encrypt with Certbot, or integrating with a cloud provider's certificate manager) to handle certificate issuance and renewal. This prevents expired certificates, a common cause of connection failures.
- Centralized Certificate Management: For environments with many
apiendpoints andgatewayinstances, use a centralized system orapi gateway(like ApiPark) to manage certificates. This ensures consistency and simplifies deployment. - Monitor Certificate Expiration: Set up monitoring and alerts for certificate expiration dates well in advance. Tools and platforms often have this built-in.
- Full Chain Deployment: Always ensure your servers are configured to send the complete certificate chain (server certificate + all intermediate CA certificates) to clients. Never rely on clients to have intermediate CAs pre-installed (unless it's a very specific, closed environment).
- Use Reputable CAs: Stick to widely trusted Certificate Authorities. This minimizes issues with clients not trusting the root CA.
- Regularly Review TLS Configurations: Periodically review server TLS configurations for security best practices (e.g., strong cipher suites, up-to-date TLS versions, HSTS).
- Test Thoroughly: After any certificate update or TLS configuration change, use
openssl s_client(from various client environments if possible) to verify correct certificate display and chain validation.
Summary Table of openssl s_client Options for Certificate Debugging
Here's a quick reference for common openssl s_client options useful for diagnosing certificate issues:
| Option | Description | Primary Use Case |
|---|---|---|
-connect host:port |
Specifies the target hostname or IP address and port for the TLS connection. | Essential for initiating any connection. |
-servername hostname |
Sends the Server Name Indication (SNI) extension during the Client Hello. The hostname should match the domain name you are trying to connect to. |
Crucial for connecting to virtual hosts on servers hosting multiple domains, ensuring the correct certificate is presented. Addresses SNI-related certificate display issues. |
-showcert |
Instructs openssl s_client to print the entire certificate chain received from the server, regardless of verification status. |
Verifying which certificates the server is actually sending. Essential for diagnosing missing intermediate certificates or incorrect server certificates. |
-CAfile path/to/ca.pem |
Specifies a file containing a bundle of trusted CA certificates in PEM format. openssl s_client will use these to verify the server's certificate chain. |
Trusting custom or enterprise CAs, or overriding the default system trust store. Useful when a certificate chain can't be validated against system CAs. |
-CApath path/to/dir |
Specifies a directory containing trusted CA certificates. Certificates in this directory must be named using their subject hash and symlinked to the actual certificate files. | Similar to -CAfile, but for a collection of individual CA files. Often used in specific system configurations. |
-cert client.crt |
Specifies the client's public certificate file (in PEM format) to be sent for client authentication. Requires -key as well. |
Debugging mutual TLS (mTLS) connections where the server requires client authentication. |
-key client.key |
Specifies the client's private key file (in PEM format) corresponding to the client certificate provided with -cert. |
Debugging mTLS connections. |
-tls1_2, -tls1_3 |
Forces openssl s_client to only use a specific TLS protocol version (e.g., TLS 1.2, TLS 1.3). Other versions like -ssl3, -tls1, -tls1_1 are mostly for testing legacy systems (and are insecure). |
Troubleshooting TLS version incompatibility issues or verifying server support for specific TLS versions. Helps determine if an older server is causing issues with modern clients or vice-versa. |
-ciphers SUITE |
Specifies a list of allowed cipher suites for the TLS handshake. | Diagnosing cipher suite incompatibility issues, particularly in restrictive environments or when trying to identify unsupported/deprecated ciphers on the server. |
-debug, -msg, -state |
Provides increasingly verbose output about the TLS handshake process. -debug shows raw bytes, -msg shows protocol messages, -state shows SSL engine state changes. |
Deep-dive analysis of the TLS handshake. Indispensable for pinpointing the exact point of failure, unexpected messages, or truncation of the handshake, especially when -showcert doesn't provide enough context. |
-quiet |
Suppresses most of the diagnostic output, only showing the final results and errors. | For scripting or quick checks when you only care about success/failure and return codes, without verbose handshake details. |
-verify_return_error |
Makes OpenSSL return a non-zero exit code if certificate verification fails, even if the connection otherwise establishes. Useful for scripting automated checks. | Automated health checks and CI/CD pipelines to ensure certificate validity. |
Conclusion
The openssl s_client -showcert command is a powerful diagnostic tool, but its utility hinges on a thorough understanding of TLS, certificate chains, and its specific operational nuances. When the expected certificate doesn't appear, or the chain is incomplete, it's not a failure of openssl itself, but rather an indication that deeper issues are at play—be it SNI mismatches, server misconfigurations (like missing intermediate certificates), network proxies, or even fundamental TLS version incompatibilities.
By methodically investigating the common causes detailed in this article, leveraging advanced debugging flags like -debug and -msg, and adopting sound certificate management practices, you can effectively troubleshoot and resolve these elusive problems. Remember that robust api gateway solutions, such as ApiPark, play a crucial role in automating and centralizing certificate management, significantly mitigating many of these issues before they impact your api consumers. Mastering openssl s_client empowers you to maintain secure, trustworthy connections across your entire digital infrastructure, from individual api endpoints to complex api gateway deployments. The path to secure and reliable communication begins with a clear understanding of its foundational elements, and openssl provides the lens through which to examine them.
Frequently Asked Questions (FAQs)
1. What does Verify return code: 21 (unable to get local issuer certificate) mean after running openssl s_client -showcert? This error typically means that openssl could not find a trusted certificate authority (CA) that issued one of the certificates in the server's chain, or more commonly, that the server failed to send all necessary intermediate certificates. The client received an incomplete chain, and thus couldn't build a path to a trusted root CA in its local trust store. To fix this, ensure the server is configured to send the full certificate chain (server cert + all intermediates), or use the -CAfile or -CApath options to point openssl to the correct trusted CA certificates.
2. Why does openssl s_client -showcert show a different certificate than what I expect for my domain? This is most often due to Server Name Indication (SNI) issues. If a server hosts multiple websites/domains on a single IP address, it relies on the SNI extension in the client's "Client Hello" to know which certificate to present. If you omit the -servername flag or provide an incorrect one, the server might send its default certificate, which may not be the one you're expecting for your specific domain. Always use openssl s_client -servername your.domain.com -connect your.domain.com:443 to ensure the correct certificate is requested.
3. Can openssl s_client -showcert detect if a network proxy is intercepting my TLS connection? Yes, it can often help. If you suspect a Man-in-the-Middle (MITM) proxy, run openssl s_client -showcert against your target. If the Subject and Issuer fields of the displayed certificate (especially the first one in the chain) belong to an entity other than your expected Certificate Authority (e.g., "Corporate Security Proxy CA" instead of "Let's Encrypt" or "DigiCert"), then your connection is likely being intercepted. The output will show the proxy's certificate, not the original server's.
4. How can APIPark help prevent certificate display issues when using openssl s_client against my api endpoints? ApiPark is an API gateway and management platform that centralizes certificate management for your APIs. By using APIPark, you can configure and manage TLS certificates for all your api endpoints from a single interface. This helps ensure that certificates are correctly provisioned, full chains are deployed, and renewals are handled automatically, reducing the common misconfigurations that lead to openssl s_client -showcert issues. It standardizes the security posture, making it less likely for individual api services to have an incomplete or expired certificate that would trouble openssl's verification.
5. I'm testing a very old server; how do I make openssl s_client use older TLS versions? For compatibility testing with legacy systems, you might need to force openssl s_client to use older TLS versions. You can do this with flags like -tls1_2 (for TLS 1.2), -tls1_1 (for TLS 1.1), or even -tls1 (for TLS 1.0) and -ssl3 (for SSL 3.0, which is highly insecure and deprecated). For example: openssl s_client -showcert -tls1_2 -servername legacy.example.com -connect legacy.example.com:443. Be cautious, as older TLS versions have known security vulnerabilities and should not be used in production environments unless absolutely necessary, and only with appropriate risk mitigation.
🚀You can securely and efficiently call the OpenAI API on APIPark in just two steps:
Step 1: Deploy the APIPark AI gateway in 5 minutes.
APIPark is developed based on Golang, offering strong product performance and low development and maintenance costs. You can deploy APIPark with a single command line.
curl -sSO https://download.apipark.com/install/quick-start.sh; bash quick-start.sh

In my experience, you can see the successful deployment interface within 5 to 10 minutes. Then, you can log in to APIPark using your account.

Step 2: Call the OpenAI API.